In this article we take a look at a phishing campaign that pretends to be an "Unusual sign-in activity" alertfrom Microsoft that could easily trick someone into clicking on the enclosed link.
With companies such as Google and Microsoft commonly sending users alerts when unusual activity has been discovered on their account, users may feel its normal to receive them and would then click on the enclosed link.
Attackers are capitalizing on this by sending emails that pretend to be "Microsoft account unusual sign-in activity" alerts from Microsoft. When compared to the legitimate email notifications sent by Microsoft, they look almost identical with the same information fields and even the same sender address of "account-security-noreply@accountprotection.microsoft.com".
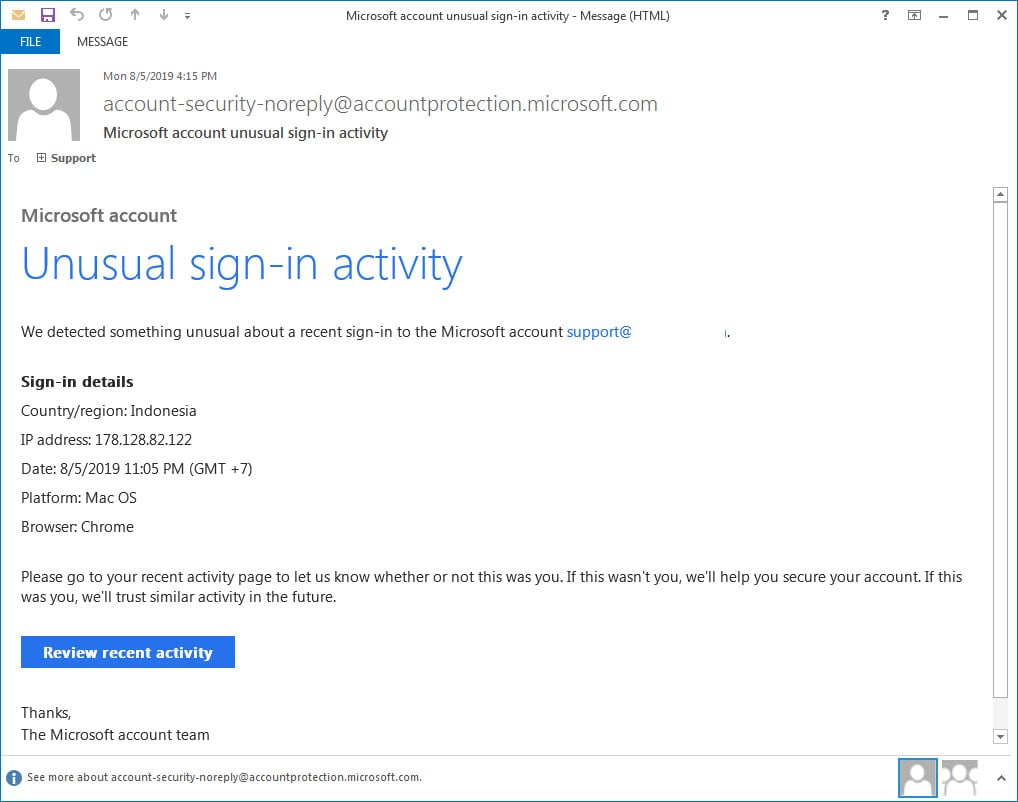
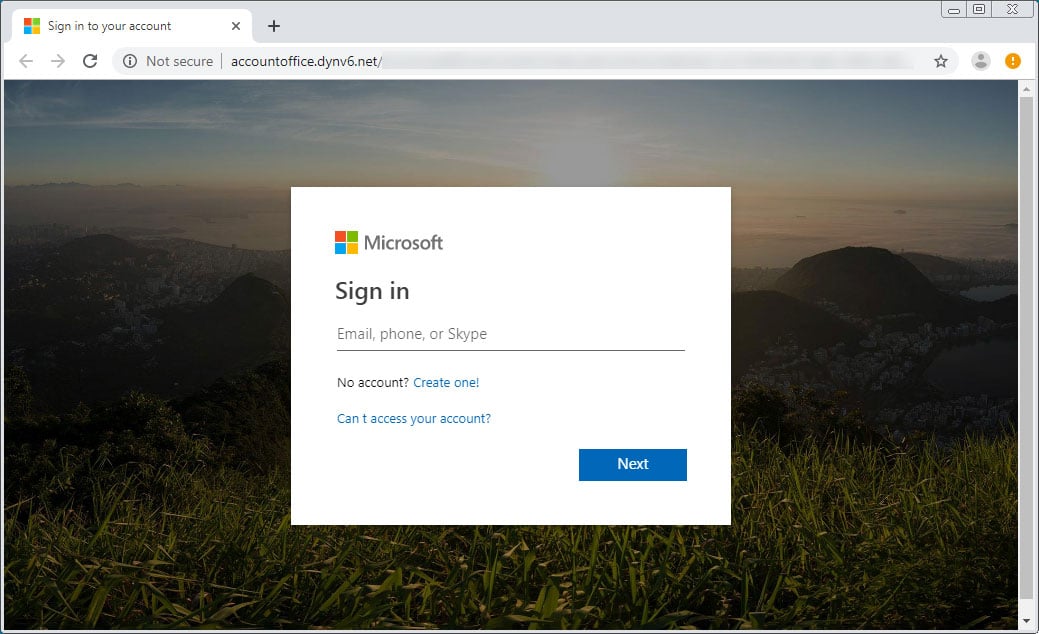
What's different, though, is that when you click on the "Review recent activity" email link, instead of going to Microsoft to review your account's sign-in activity, you are brought to a fake landing page on a non-Microsoft site that asks you to login.
When a victim enters their credentials, the information will be saved for the phishers to retrieve later so that they can access your account.
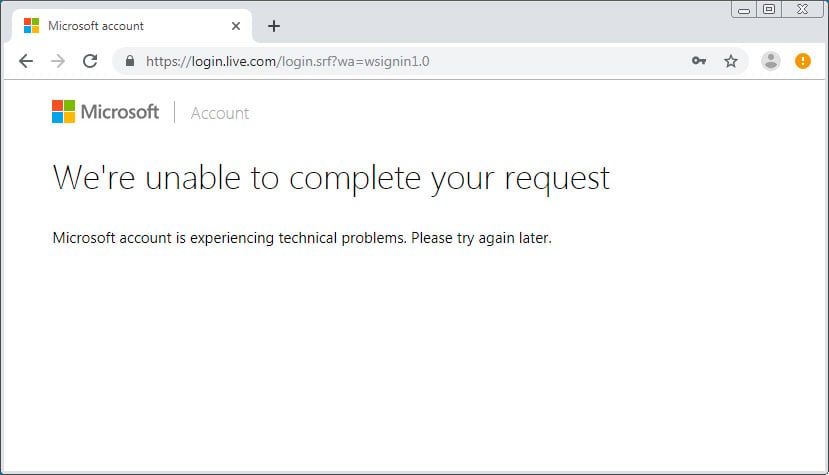
No matter what credentials are entered in the fake login form, the user will always be redirected to an error page on Microsoft's live.com site. This is to make it look like there is a problem with your account and that nothing strange is going on.
While some users may have felt that the emails are safe because they are coming from a legitimate Microsoft email address, it is always important to remember that the From email address can always be spoofed to be from any account an attacker wants.
Therefore, even if a phishing email looks legitimate, it is important to pay attention to the URLs of the landing pages before entering your login credentials in a displayed login form.


Comments
doncoyote - 4 years ago
Use your own bookmarks or key in your own URLs, people.
Herf - 4 years ago
I just received one of these emails. When I hover over the "Review recent activity" button, the URL I see is https://account.microsoft.com/activity
I don't know if that is an official Microsoft url or not, but if it is, can they spoof the url that is shown by a mouse hover?
sassysizzle - 2 years ago
Hello,
I received a fake email subject titled: Microsoft Account Unusual Password Activity from Microsoft account team (no-reply@microsoft.com) Email contains fake accept/rejection links. When cursor is placed over links notice.unusual.activity@gmail.com etc. is revealed instead of Microsoft address.
Example Below and Note: Do Not Click/Open links in these emails because they're usually programmed to record activity (personal data, passwords etc.).
Microsoft account unusual password activity
Microsoft account team <no-reply@microsoft.com>
Sat 12/11/2021 12:52 AM
Microsoft account
Did you attempt to change your password ?
The password for the Microsoft account XXXXXXX@outlook.com there was an attempt to change it.
If this was you, then you can safely and click yes .
Yes It was Me (notice.unusual.activity@gmail.com [additional text re yes etc.]
If this wasn't you, your account has been tried to compromised. Please click No:
No It was not Me (notice.unusual.activity@gmail.com [additional text re no etc.]
Thanks,
The Microsoft account team